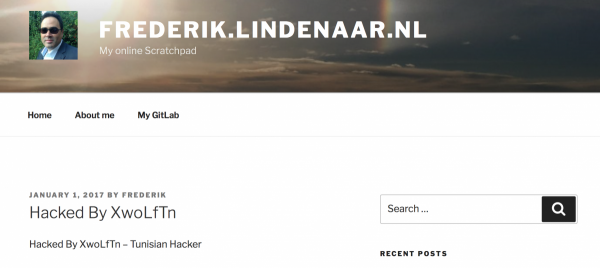
Today morning I noticed that my blog had been altered as it looked as displayed in the picture above. The first thing I did when I noticed this was to take my webserver offline until I could check what actually happened and to assess the impact of this breach of security. Fortunately the damage turned out to be very limited and easy to resolve so after a short research I was able to reconnect my webserver again and write about it.
Since I did not see any traces of altered files on the system, nothing in the logs (which I store on a separate log server so that they can’t be tampered with) and no strange things in any database (also hosted on a separate server for security reasons) I could conclude that the ‘breach’ was limited to the alteration of one blog post of this single WordPress site. When I looked at the revisions of the affected post I noticed that it actually had been altered twice, besides the modification displayed above that took place yesterday I also found another modification from one day earlier:

When I started searching on Google about security holes in WordPress I learned quickly that the guys from security firm Securi had discovered a content injection vulnerability in WordPress’ REST API (which is enabled by default as of version 4.7). The vulnerability allowed one to circumvent the security mechanism and alter existing content (i.e. posts). This is what also happened to my blog and it looks like scrip kiddies had automated this process and were trying sites at random, hence two changes on one site. Since only one of the blogs hosted on my server was affected, this does not look like a massive breach or thought-through/systematic attack. Given the content of the altered posts it also did not really look like a massive professional attack on my servers but merely people seizing the opportunity to alter still-unpatched WordPress installations.
This issue was reported to WordPress development on January 20th and a fix for it was silently included in WordPress version 4.7.2 that was released on January 26th. On Februari 1st the WordPress development team fully disclosed the issue and the process they had followed. Looks like it was taken very seriously and dealt with in the right way, great job guys!
It turns out I had missed out on an important update that became available more than a week ago. In the mean time the script kiddies cold do what they did. That’s my bad and also both the risk with using widely used software like WordPress as a security vulnerability will be picked up immediately by many to be exploited once it is disclosed. However, the advantage is that issues will be found more quickly and fixes also become available quicker, which is a clear advantage that outweighs the risk/disadvantage. To avoid this from happening again I have now subscribed to the WordPress Security RSS feed to ensure I won’t miss something like this again.